Protect Everything
You Build and Run
Wiz connects code, cloud, and runtime into a single security graph that provides the end-to-end context required to automate risk reduction and threat response, enabling security teams to operate at AI speed. AI alone doesn't make security faster. Context does.
Trusted by more than 50% of Fortune 100 companies
Anewdevelopmentreality.
A new challenge for security
A new challenge for security
Traditional security was built for a slower era
scanning code, cloud, and runtime in silos, with manual correlation and human-driven processes across teams.
That approach doesn't scale in the AI era
where applications change constantly and attackers use AI to analyze code, infrastructure, and runtime as one system to find a path in.
Security, re-built for the AI era
Security must move as fast as development - understanding applications, continuously analyzing risk, responding to threats, and fixing issues in code. Security becomes continuous and automated, aligned with how modern software is built. Wiz makes this possible.
A new operating model for AI-era security
Security at AI speed, powered by context.
Wiz connects code, cloud, and runtime into a unified context graph. Context enables teams to use AI to fix exploitable risks at the source, stop attacks in real-time, and start secure from the IDE – automatically and accurately.
For the first time, defenders can move as fast as attackers - without sacrificing precision or slowing innovation.
Prevent Cloud and AI Risks
Secure every application you build in the cloud, from infrastructure to data.
Learn moreRuntime protection
Runtime protection and threat detection, built for the cloud and AI era.
Learn moreWiz Green agent
Automatically turns risks into code fixes - opening PRs to fix issues at the source and helps write secure code from the start.
Wiz Red agent
Discovers every attack path with automated penetration testing and risk discovery.
Wiz Blue agent
Automates SecOps threat hunting and investigation to validate and prioritize real threats.
AI-Powered Code-to-Cloud Defense
Ready to protect your cloud?
Schedule a call with a Wiz expert
How Wiz helps: From Exposure to Code Fix
Attack surface scanning
Wiz maps externally reachable assets and models initial access paths:
Attack surface scanner (reachable, exploitable)
Effective internet-exposure of endpoints & services
Wiz Threat Research intel
Deep internal analysis
We connect code, cloud, identities, network, and runtime to model:
Lateral movement
Privilege escalation
Data access chains
FIX AT SCALE IN CODE
Using graph context and ownership mapping, Wiz:
Identifies the right place for the fix
Assigns the right owner (team, repo, service)
Generates direct code & infra fixes to code owner
DETECT AND BLOCK
Using the Wiz eBPF Runtime Sensor, combined with deep analysis of cloud and SaaS logs and rich application and code context, Wiz can:
Detect real and block exploitation attempts
Block lateral movement in progress
Investigate with full contextual lineage
How Wiz helps: From Exposure to Code Fix
Attack surface scanning
Wiz maps externally reachable assets and models initial access paths:
Attack surface scanner (reachable, exploitable)
Effective internet-exposure of endpoints & services
Wiz Threat Research intel
Deep internal analysis
We connect code, cloud, identities, network, and runtime to model:
Lateral movement
Privilege escalation
Data access chains
FIX AT SCALE IN CODE
Using graph context and ownership mapping, Wiz:
Identifies the right place for the fix
Assigns the right owner (team, repo, service)
Generates direct code & infra fixes to code owner
DETECT AND BLOCK
Using the Wiz eBPF Runtime Sensor, combined with deep analysis of cloud and SaaS logs and rich application and code context, Wiz can:
Detect real and block exploitation attempts
Block lateral movement in progress
Investigate with full contextual lineage
Trusted by security teams all over the world
Wiz secures
the AI frontier
Most frontier AI labs rely on Wiz to secure their cloud, AI workloads, and the data powering next-generation innovation.
Continuously discover AI models, agents, MCP servers, and services across cloud and SaaS.
Identify AI-specific risks — from sensitive data exposure and guardrails to exposed endpoints.
Understand real AI risk by connecting context across infrastructure, identity, data, and AI.
Detect and respond to AI runtime threats, from data exposure to malicious agent actions.
feedback
See what our users think about Wiz
Recognized market leader by top analysts
The Forrester Wave
Cloud Native Application Protection Solutions, Q1 2026
Wiz Named a Leader with the Highest Current Offering Score in The Forrester Wave™ CNAPP, Q1 2026
IDC MarketScape
Worldwide Cloud-Native Application Protection Platforms 2025
Wiz Recognized as a Leader in the 2025 IDC MarketScape for CNAPP
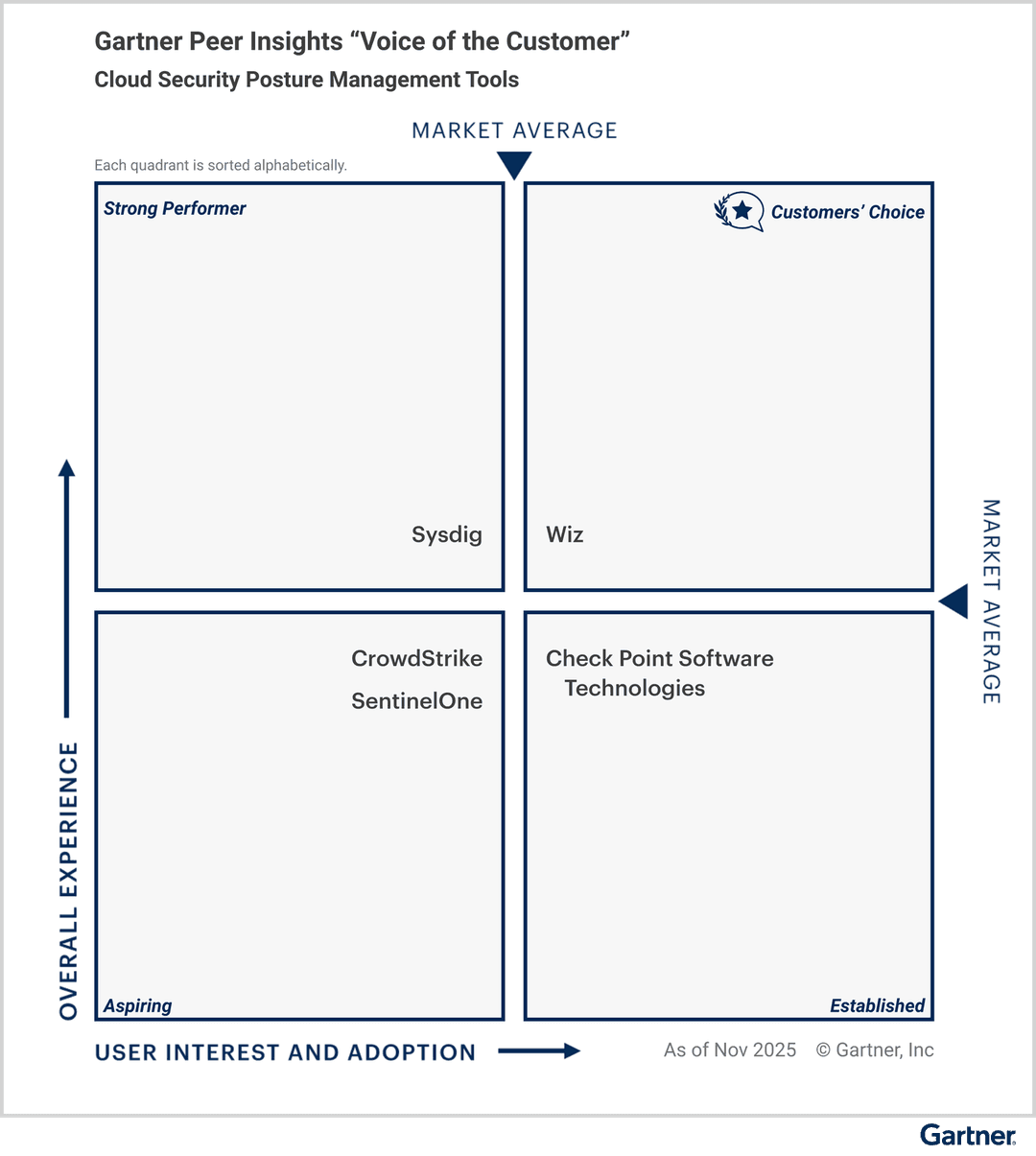
Voice of the Customer
Cloud Security Posture Management 2026
Wiz Named a Customers’ Choice for Cloud Security Posture Management Tools (CSPM)
4.7/5
792+ Reviews
4.8/5
265+ Reviews
March 2026
Driving Outcomes
Speed
"We began seeing information within 60 minutes and have now standardized to Wiz across our environment."
Erik Hart, CISO
Impact
"I have not seen anything else that can give you as big of an impact as Wiz."
Igor Tsyganskiy, Global CISO
Simplicity
"Wiz demystifies a lot of Azure, so we can understand it well enough to talk to other teams, despite not being cloud experts."
Illyan Tytel, Landscape Integrity Monitoring Senior Lead