CLOUD INFRASTRUCTURE ENTITLEMENT MANAGEMENT (CIEM)
Take Control of Your Cloud Entitlements
Wiz analyzes cloud entitlements and auto-generates least privilege policies across your cloud, to help teams visualize, detect, prioritize, and remediate identity (IAM) risks.
Rated #1 cloud security software on G2
4.7
772 reviews
Trusted by the most innovative companies in the world
Secure Your Cloud Environment
Wiz analyzes cloud entitlements and effective permissions to help teams understand their identity-related risk and exposure.
Right-Size Permissions
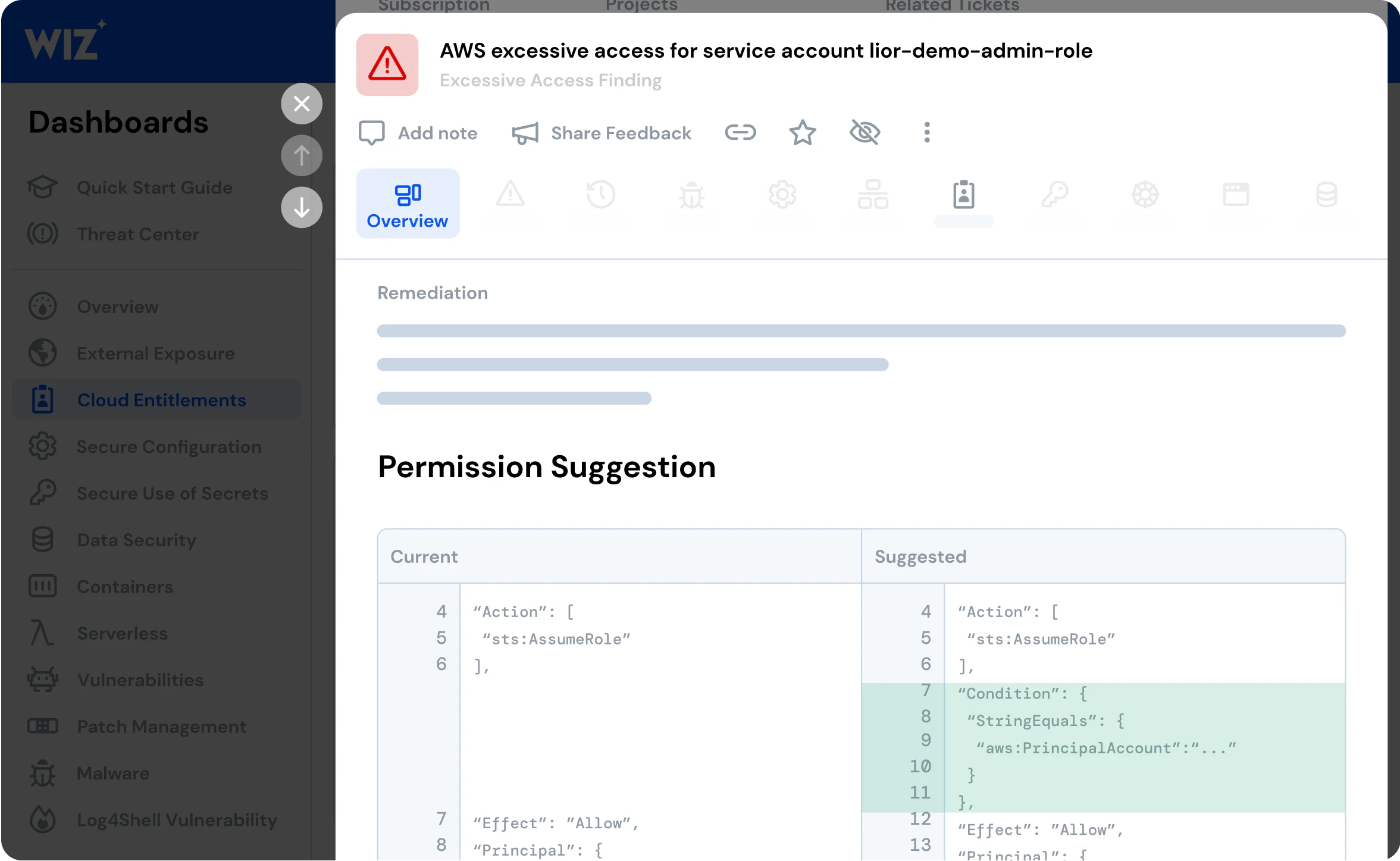
Monitor human and service identities and get auto-generated least privilege suggestions to right-size access and entitlements in your environment.
Analyze Effective Exposure
Wiz builds a map of effective access between all principals and all resources, taking into account advanced cloud-native mitigating controls including boundaries, ACLs and SCPs.
Exposed Secrets and Lateral Movement
Agentless and frictionless detection of leaked secrets or credentials that attackers might use in attempts to access sensitive assets or take over accounts.
Enforce Least Privilege Across Your Clouds
Go Beyond CIEM

The reviews are in
Customers rate Wiz #1 in cloud security
772 Reviews
WHAT OUR CUSTOMERS SAY ABOUT WIZ
Read about the value that Wiz provides leading businesses
Get a personalized demo
Ready to see Wiz in action?
"Best User Experience I have ever seen, provides full visibility to cloud workloads."
"Wiz provides a single pane of glass to see what is going on in our cloud environments."
"We know that if Wiz identifies something as critical, it actually is."