The #1 Cloud Workload Protection Platform
Scan all workloads, detect vulnerabilities in your cloud environments, and prioritize critical risks to block attack paths.
Rated #1 cloud security software on G2
4.7
772 reviews
Trusted by the most innovative companies in the world
The Leading Cloud-Native Security Platform
Get full visibility into your cloud environment and prioritize risks with context.
Proactive Attack Surface Reduction
Full-stack visibility into your entire cloud environment in minutes with agentless scanning for vulnerabilities, secrets, malware, and misconfigurations across virtual machines, containers and serverless functions so you can minimize workload risk.
Real-Time Last Line of Defense
Complete monitoring from inside the workload using the Wiz Runtime Sensor for threats and malicious behavior so your teams can respond quickly and with context to any potential unfolding threat.
One Policy Across Cloud and Code
Ensure workload issues are caught and remediated before they hit production by shifting security left during the software development cycle.
Quickly Identify and Prioritize Vulnerabilities
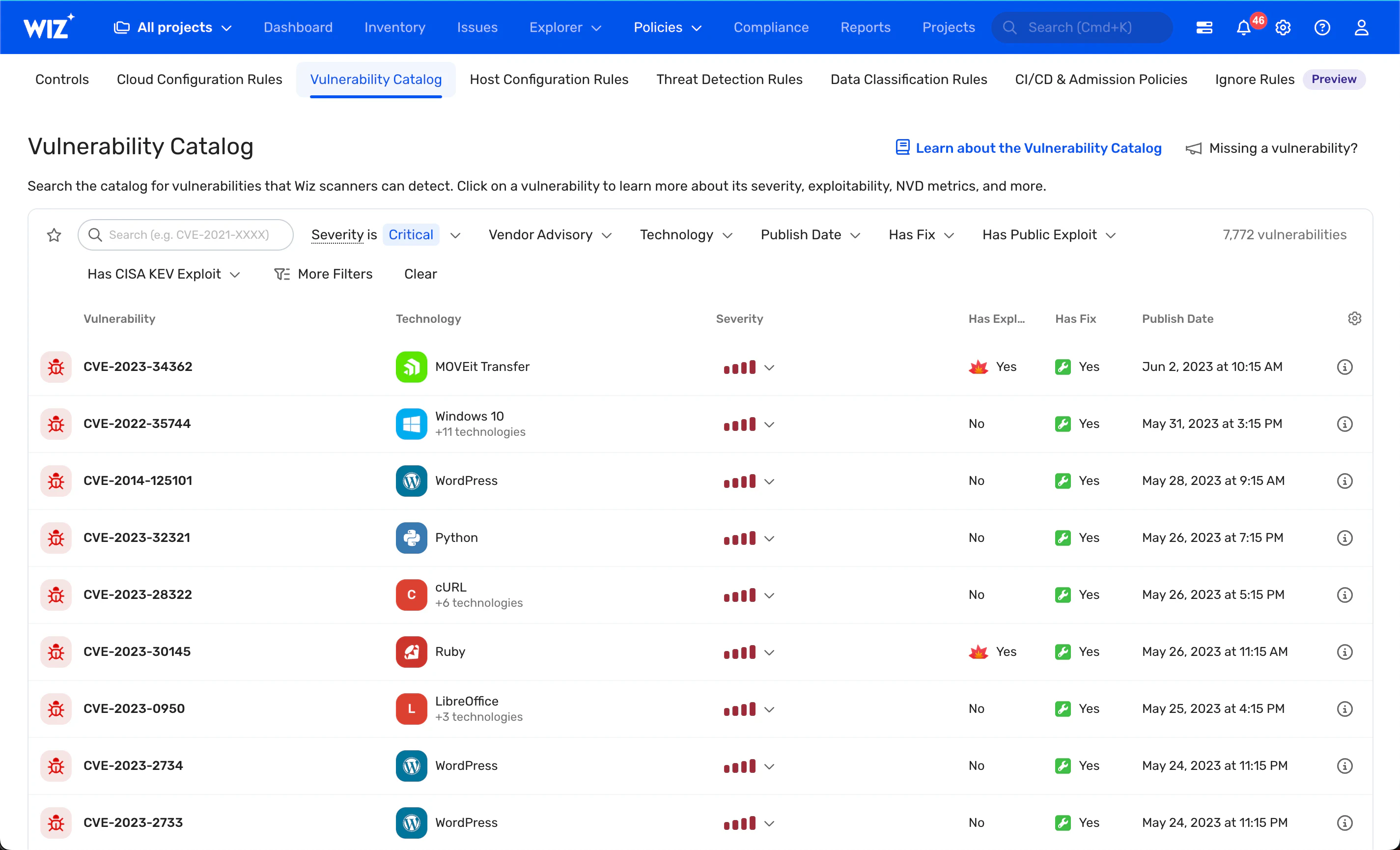
Get Deep Assessments
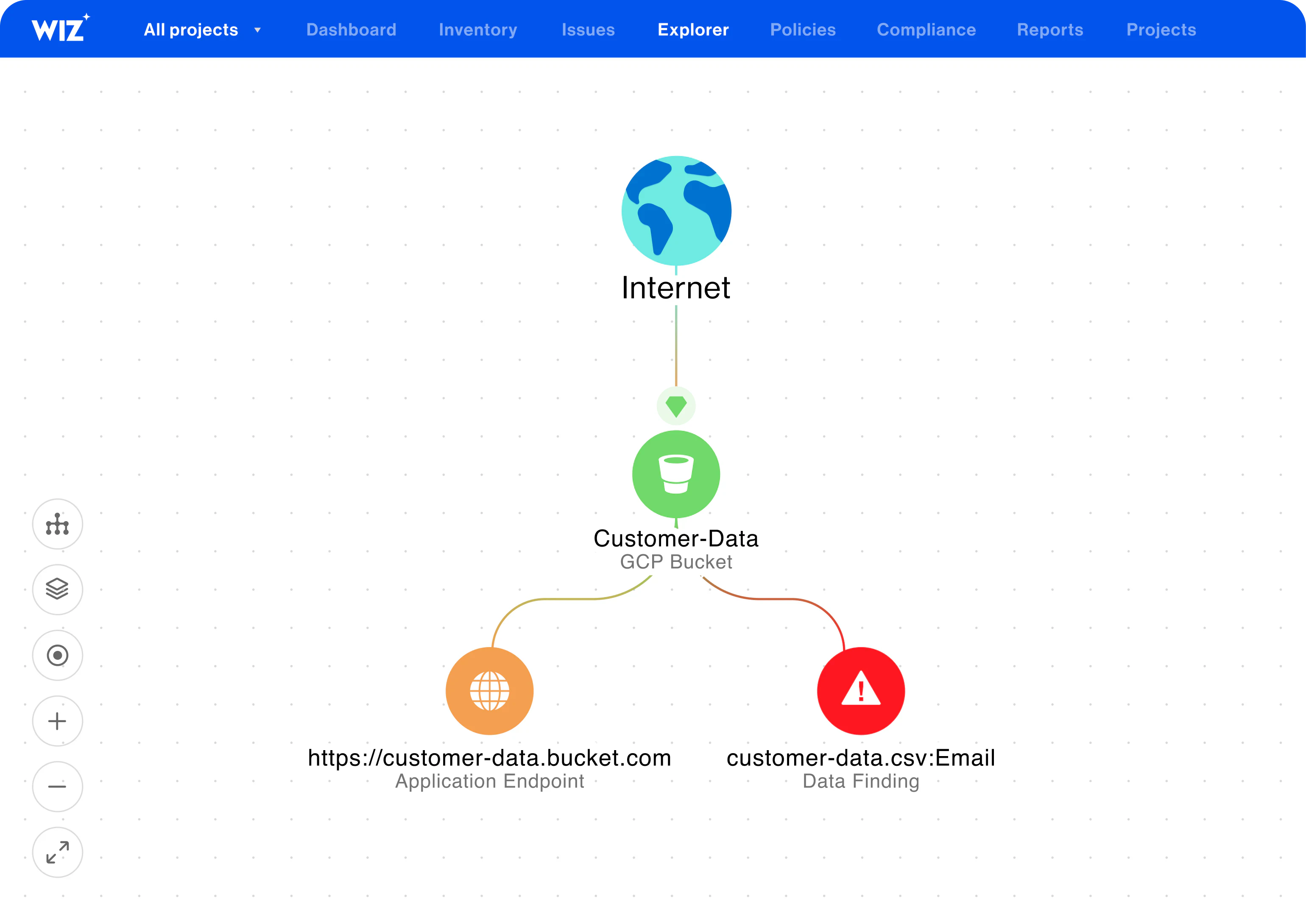
Improve Prioritization with Context and Visualization

Get Complete Workload Visibility
Agentless discovery of workloads: Discover all workloads running on the cloud without deploying agents across all major cloud vendors.
Analyze any cloud workload: Analyze any cloud workload: Analyzes all cloud workloads including virtual machines,ephemeral resources, container registries, serverless functions, and virtual appliances.
Analyze all layers: Analyze all layers of your configuration including cloud, operating system, host, and application.
The reviews are in
Customers rate Wiz #1 in Cloud Security
772 Reviews
WHAT OUR CUSTOMERS SAY ABOUT WIZ
Read about the value that Wiz provides leading businesses
Get a personalized demo
Ready to see Wiz in action?
"Best User Experience I have ever seen, provides full visibility to cloud workloads."
"Wiz provides a single pane of glass to see what is going on in our cloud environments."
"We know that if Wiz identifies something as critical, it actually is."