DATA SECURITY POSTURE MANAGEMENT (DSPM)
Integrated Data Exposure Protection
Continuously monitor for sensitive data and secrets exposure and proactively eliminate attack paths to prevent data breaches.
Rated #1 cloud security software on G2
4.7
792 reviews
Trusted by the most innovative companies in the world
Protect Your Most Critical Data
Wiz scans and alerts of exposure paths to sensitive data including PII, PHI, PCI, and secrets across public and private buckets, hosted database servers such as MySQL and MongoDB, cloud-managed SQL databases such as AWS RDS, Azure SQL, and GCP Cloud SQL, as well as Amazon DynamoDB, Google BigQuery, Amazon Lightsail, and OpenAI
Discover your sensitive data
Rapid, agentless visibility into critical data in your buckets, data and OS volumes, and managed and hosted databases with pre-defined and custom classifiers to easily answer the question of what data is located where.
Put your data in context
Automatically correlate your sensitive data with underlying cloud context, including public exposure, identities and entitlements, and vulnerabilities to understand who can access what data, how data assets are configured and used, and how data moves within your environments.
Prioritize exposure to speed response
With fully integrated DSPM, the Wiz Security Graph automatically alerts you when toxic combinations of risks create attack paths to your sensitive data so your teams can focus on the highest priority issues before they become breaches.
Start with Prevention
Traditional siloed tools completely miss complex data risks and can't detect attack paths to critical data as they form. Wiz gets you ahead of data exposure with a comprehensive platform that dramatically reduces the time it takes to identify and fix data issues.
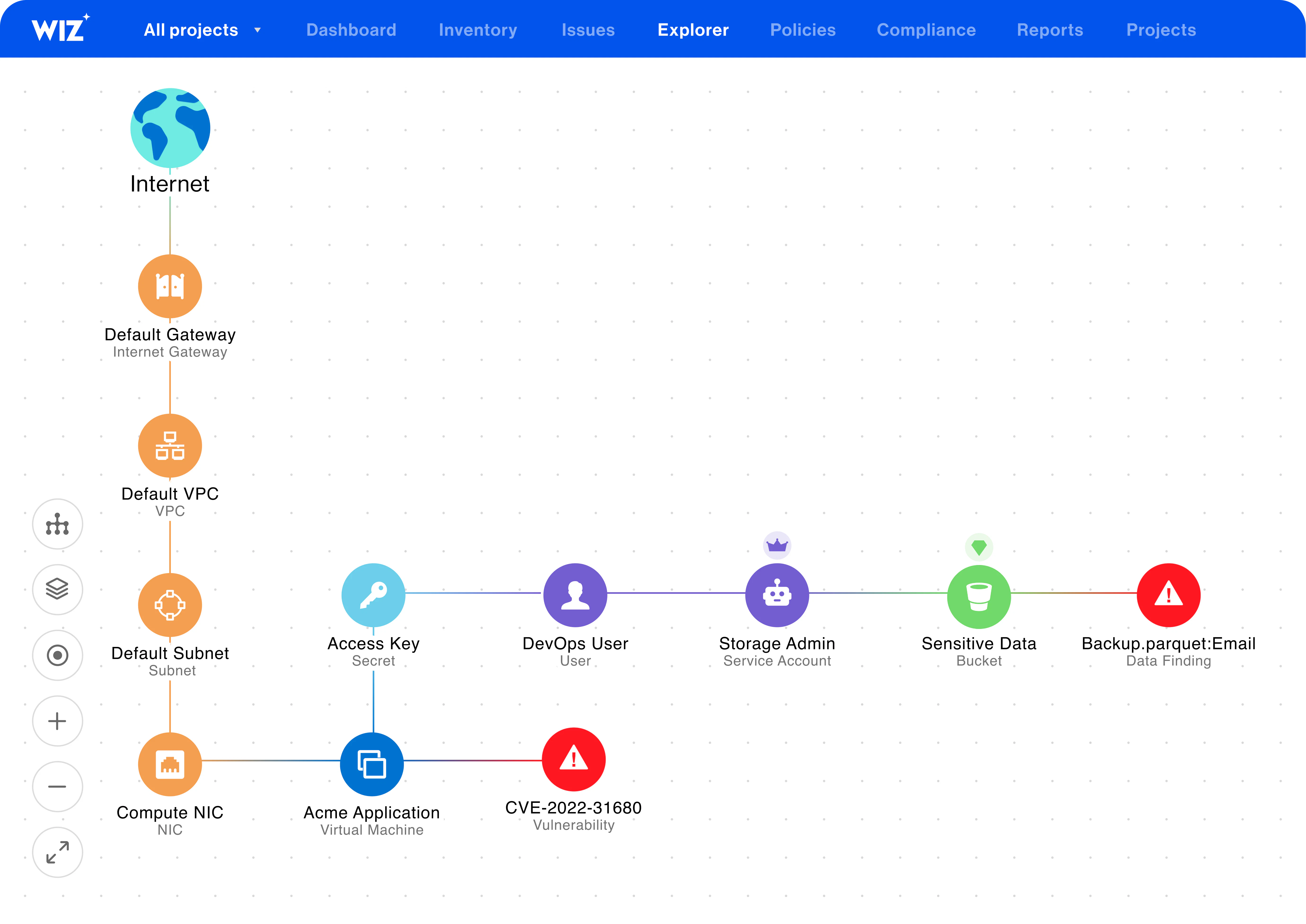
Attack path analysis
Automatically uncover attack paths to sensitive data that is validated to be publicly exposed to the internet or can be exfiltrated using a lateral movement path.
Data risk prioritization
Focus your teams on what is critical with a single prioritized queue of data issues ranked by severity and type.

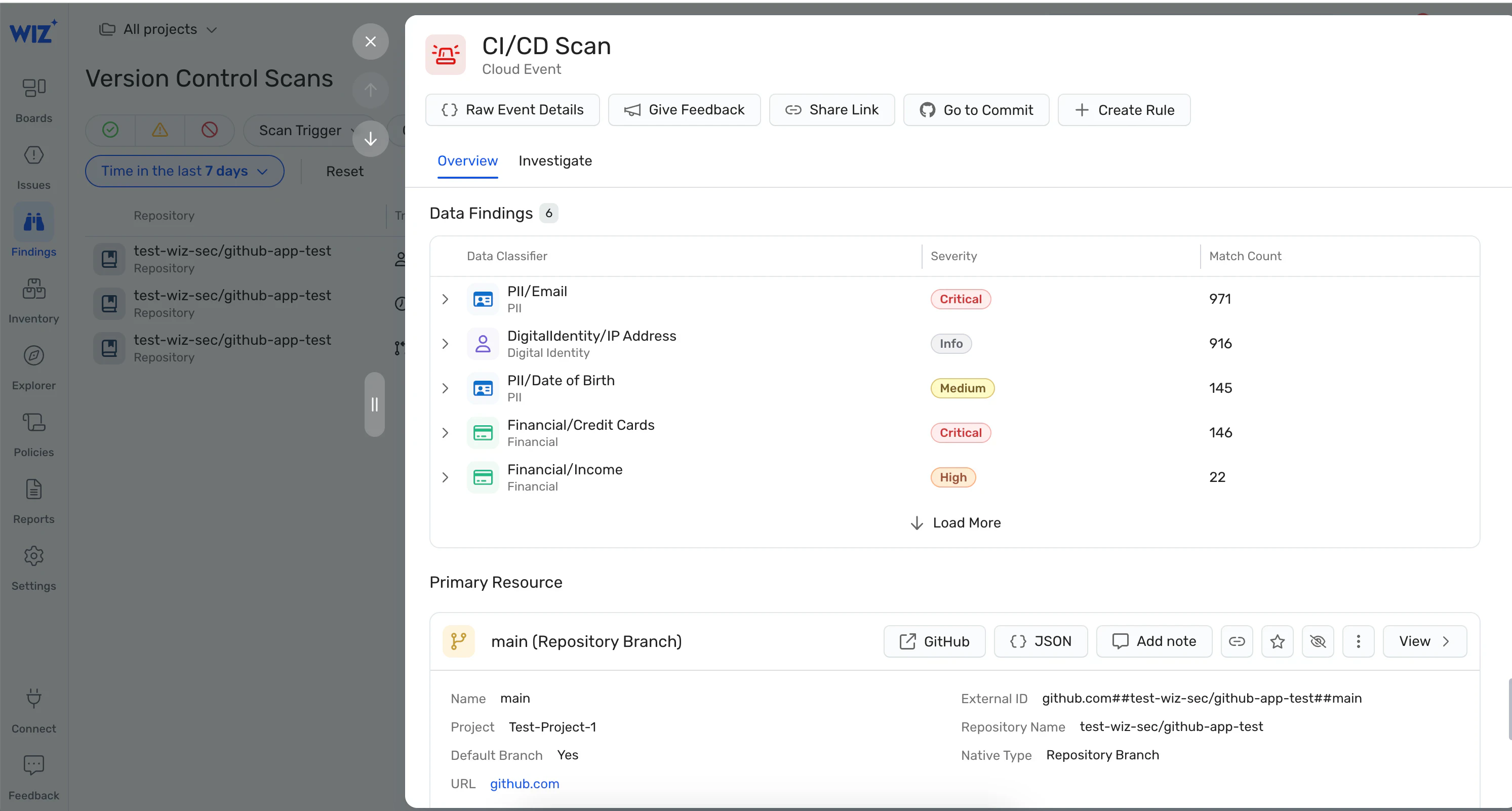
Data security for code
Identify sensitive data in development environments (IDEs), code base, pull requests, and CI/CD platforms and reduce the risk of accidental data exposure.
Continuous Data Security and Compliance
Manage security posture: Assess data security posture against pre-built data policies or write custom policies based on your business requirements.
Real-time remediation: Automatically trigger alerts and kick off remediation workflows to the relevant teams when policies are violated.
Automate compliance: Address compliance requirements using industry standard or custom-built frameworks by business unit or application.
The reviews are in
Customers rate Wiz #1 in cloud security
792 Reviews
WHAT OUR CUSTOMERS SAY ABOUT WIZ
Read about the value that Wiz provides leading businesses
Get a personalized demo
Ready to see Wiz in action?
"Best User Experience I have ever seen, provides full visibility to cloud workloads."
"Wiz provides a single pane of glass to see what is going on in our cloud environments."
"We know that if Wiz identifies something as critical, it actually is."